When interacting with software, as if in a Linux or Windows environment, a digital signature is used to authenticate the software package. It is a hashed payload message, which is additionally encrypted with a private key in a second preparation step. Thus, the private key ensures the authenticity and the hash the integrity of the transmitted message. But it happens that in the work of any software there are errors, let's consider possible on the example of GPG crypto-packet!
How to fix GPG error "NO_PUBKEY"?
It's a fairly common problem when updating a repository, when after a package manager command with the update function, a similar problem is thrown:
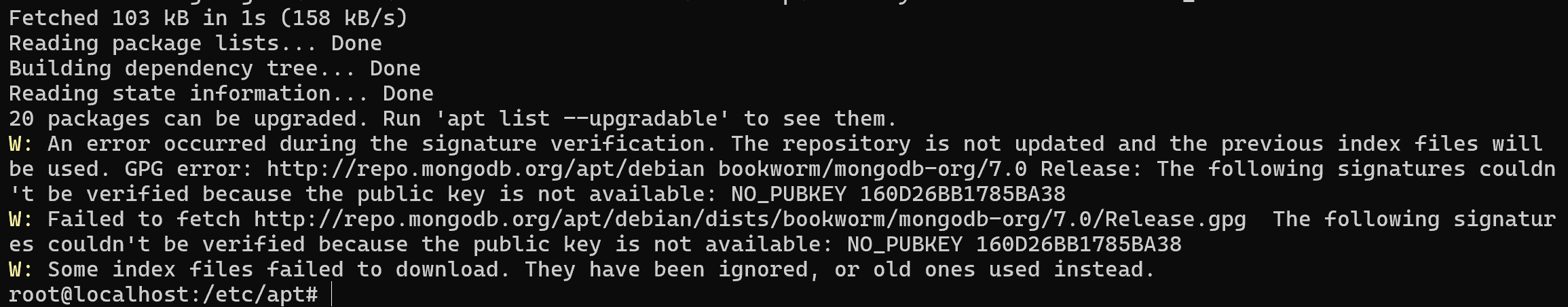
The error states that the public key 160D26BB1785BA38 was not found for the mongodb-org repository, which is used to verify the digital signature on packages in the repository. By default, Linux distributions do not allow installing packages without the corresponding key.
On the servers Serverspace cloud platform, also used keys to identify package by default. That provide seamless deployment, also you can skip this step if you have a cloud server. To create the node we need to find the cloud platform from the left menu which you can choose depending on your requirement. We choose vStack or VMware platform and click on Create Server button.
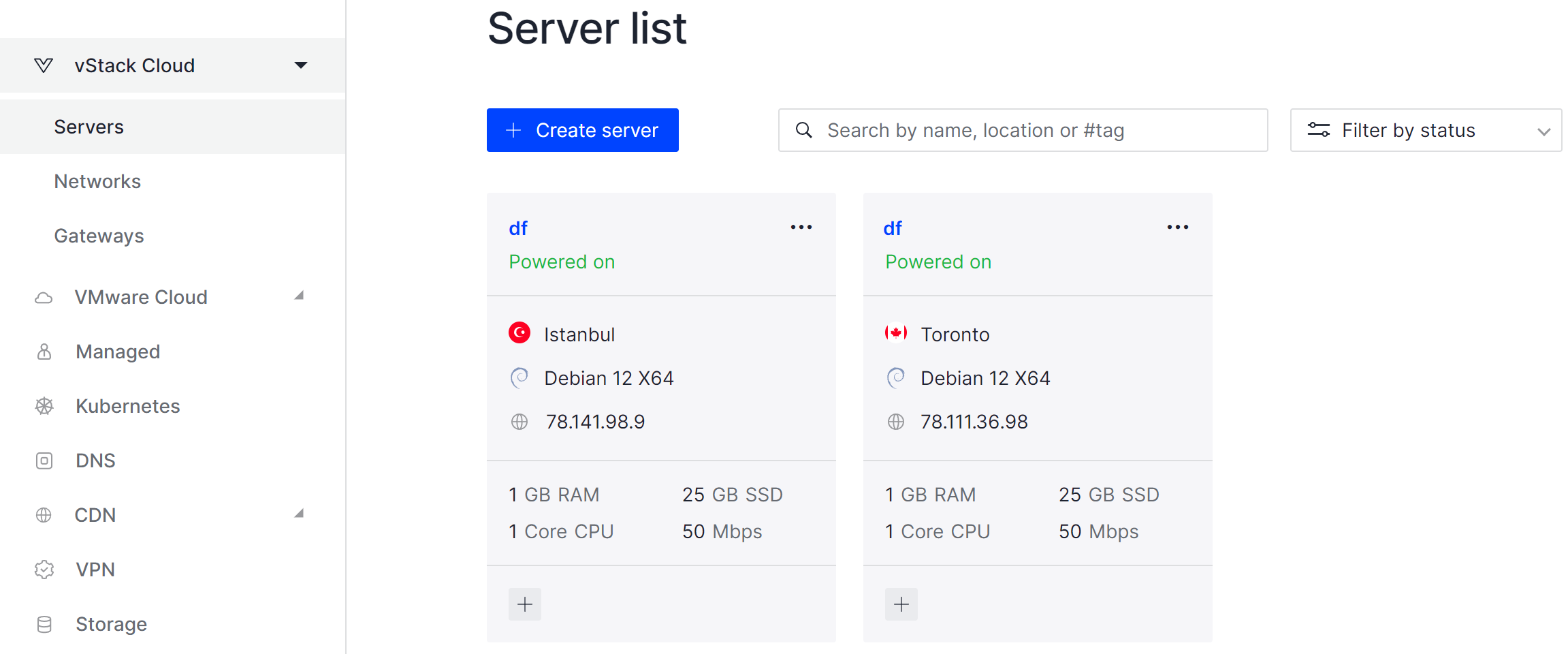
It will take some time to deploy server capacity. After that you can connect in any of the convenient ways. Let's return to our terminal with issue and explain nature of them.
Since Linux distributions do not allow you to install packages without a public key, you need to add one. There are two ways: find a file with a public key on the company's website or use a key server. For the first way, let's find the key on the company's website.
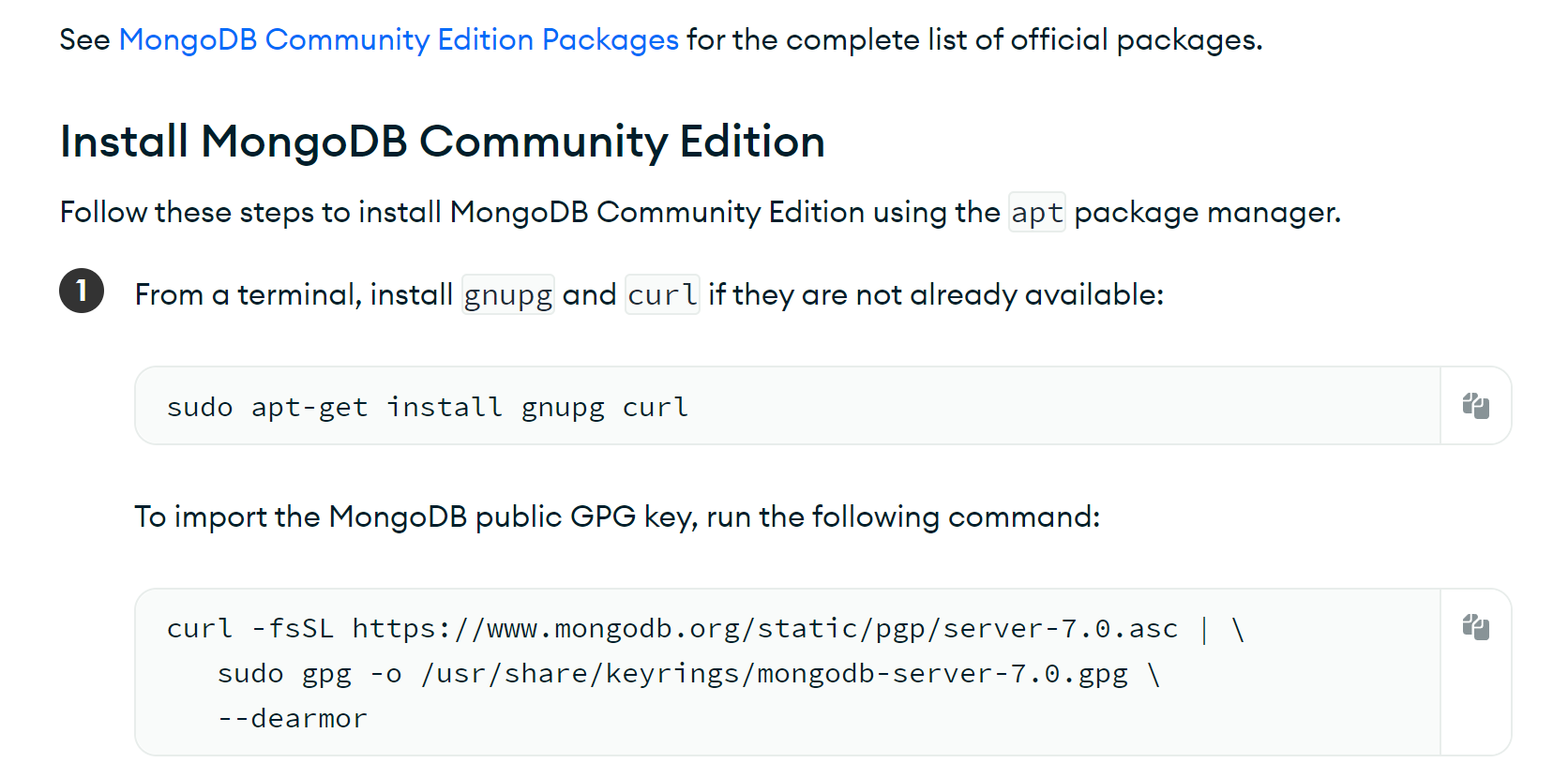
It suggests downloading the key via HTTPS, which may be a secure solution as the authentication center validates the authenticity of the site through a certificate and TLS provides a confidential channel to transmit the message.
If we trust the CA, then this method is convenient. Let's execute the command to install the necessary software:
apt install gnupg curl And then download the necessary package by converting asc to gpg format, saving it in the folder /usr/share/keyrings/mongo.gpg. To do this, run the command:
curl -fsSL https://www.mongodb.org/static/pgp/server-7.0.asc \
| sudo gpg -o /usr/share/keyrings/mongodb-server-7.0.gpg --dearmor Or we can perform this action with the help of a key server, knowing the public key identifier. The error shows the sequence 160D26BB1785BA38, which is the key identifier. Let's address the server with the command:
sudo gpg --homedir /tmp --no-default-keyring --keyring /usr/share/keyrings/mongo.gpg --keyserver keyserver.ubuntu.com --recv-keys 160D26BB1785BA38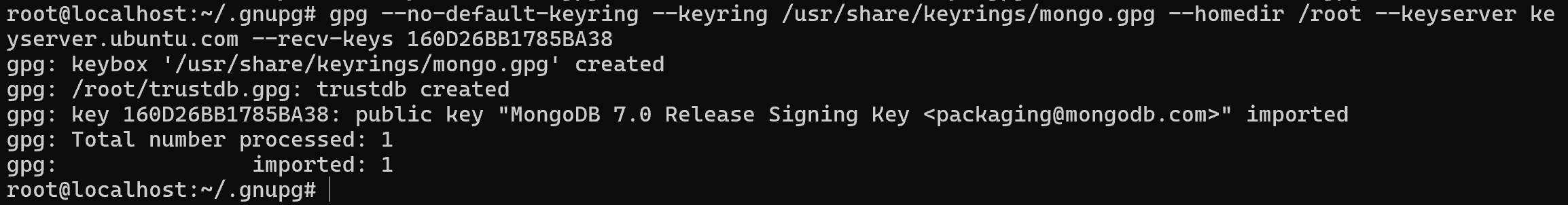
In this case, we are requesting keys from an official server that has signed them and confirmed the integrity of the keys. Parameters in the command:
- --no-default-keyring --keyring allows you to define a new keyring that will be separate from the primary keyring;
- --keyserver allows you to specify the server that will be used to request the key. You can specify any server you trust;
- --recv-keys specifies the identifier of the requested key.
Now we need to write the path to the key in the list of repositories, to communicate with each other. To do this, let's go to the file:
echo "deb [ signed-by=/usr/share/keyrings/mongo.gpg ] http://repo.mongodb.org/apt/debian bookworm/mongodb-org/7.0 main" > /etc/apt/sources.list.d/mongodb-server-7.0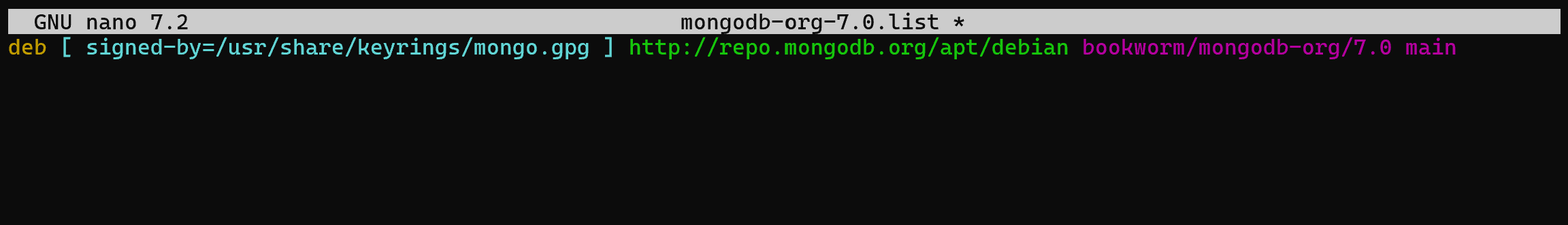
After that, you need to update the list of repositories with the command:
apt update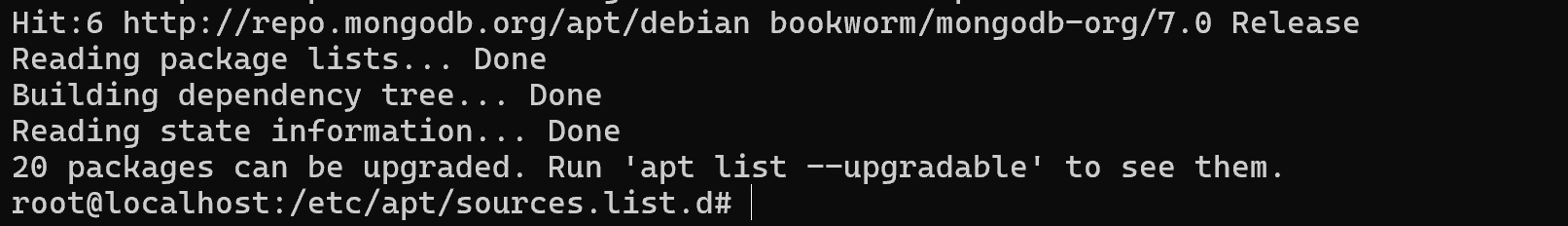
As you can see on the screenshot, the repository has been Hit, so it is now available for downloading packages. However, after adding a key, there may be a warning about the danger of using such a key.
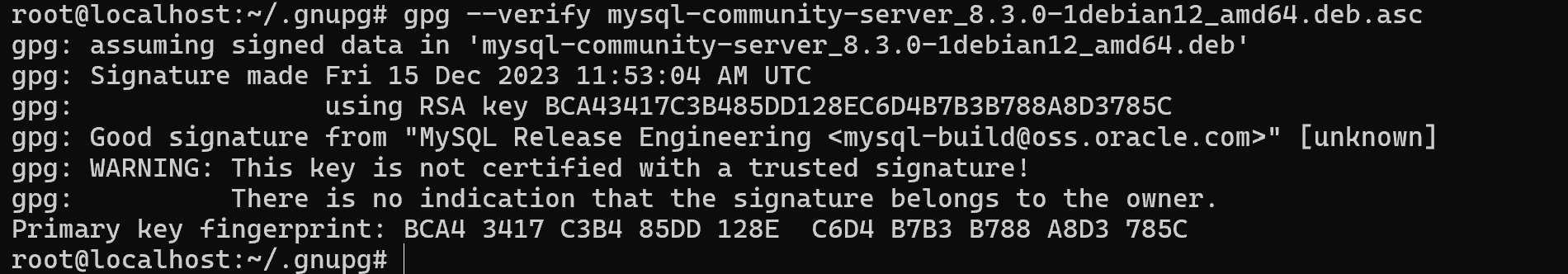
GPG: There is no indication that the signature belongs to the owner.
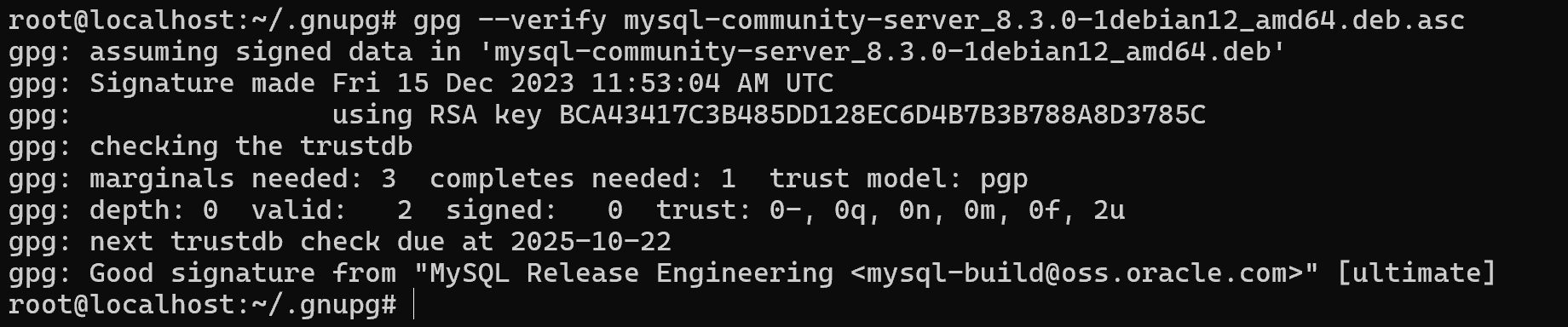
The point is that GPG uses a policy similar to certificate authorities. For a key to be considered trusted, it must be downloaded from a key server. Or the same key must be signed by a trusted key, which means it is in the trusted.gpg database with a trust level of 4-5. So, when signing such notifications are absolutely normal, but it is necessary to double-check the owners, hash sums. They will make sure that the integrity of the data transmitted from the servers.
If you are sure that the keys are legitimate, you should write the command:
gpg --edit-key 160D26BB1785BA38 Where instead of 160D26BB1785BA38, your key identifier will be specified, after which the menu of interaction with the key will open. It is necessary to specify the trust item and select the trust level:
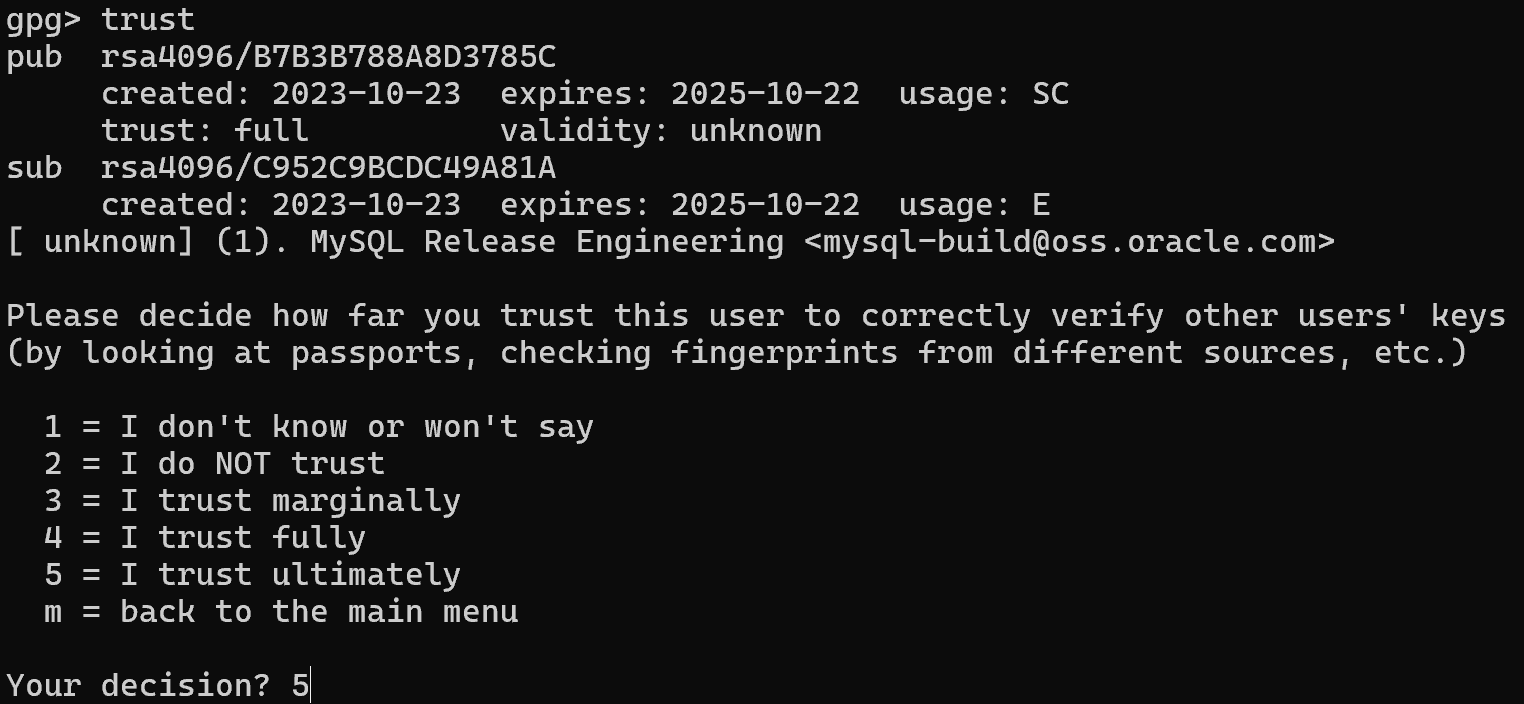
After that, the inscription will disappear when you use the key:
Troubleshooting GPG errors is an important aspect of ensuring the security and stability of operating systems, especially in the Linux world. Understanding the causes and solutions to GPG issues helps ensure the integrity and authenticity of installed software and updates. By checking keys, updating repositories, and tweaking configuration files, issues can be effectively addressed. Remember, careful troubleshooting and following the recommendations of the community of experts will help you keep your system up and running and secure.
Conclusion
GPG errors can disrupt package management and pose a potential risk if ignored. By understanding the causes—such as missing public keys, untrusted signatures, or repository misconfigurations—you can quickly restore the ability to securely update and install software on your Linux system. Adding keys via a trusted source, verifying signatures, and updating repository paths ensures the integrity and authenticity of all installed packages, keeping your system stable and secure. Regular attention to GPG error resolution is a proactive way to prevent installation failures and maintain system trustworthiness.
FAQ
- Q1: What does a GPG error mean in Linux?
A: It indicates a problem with verifying the authenticity of a software package, usually due to a missing or untrusted public key. - Q2: How do I fix the “NO_PUBKEY” error?
A: You can add the missing public key either by downloading it from the official website or retrieving it from a trusted key server using the key ID. - Q3: Can I ignore GPG warnings?
A: It is not recommended, as ignoring warnings may compromise system security. Always verify keys before trusting them. - Q4: How do I check if a key is trusted?
A: Use the command gpg --edit-key <KEY_ID> and set the trust level appropriately. A level of 4–5 indicates a fully trusted key. - Q5: Why do I still get warnings after adding a key?
A: Warnings may appear if the key is not signed by a trusted key or is not in your trusted.gpg database. Verify the key’s source and signature to resolve this. - Q6: Do GPG errors affect updates on all Linux distributions?
A: Yes, GPG errors can appear on any distribution that uses signed repositories, including Debian, Ubuntu, and their derivatives.



