Introduction
This guide explains how to configure and manage UFW (Uncomplicated Firewall) on Ubuntu servers. You will learn how to enable the firewall, create and delete rules, manage service profiles, and secure both IPv4 and IPv6 network traffic.
sudo apt update && sudo apt install ufw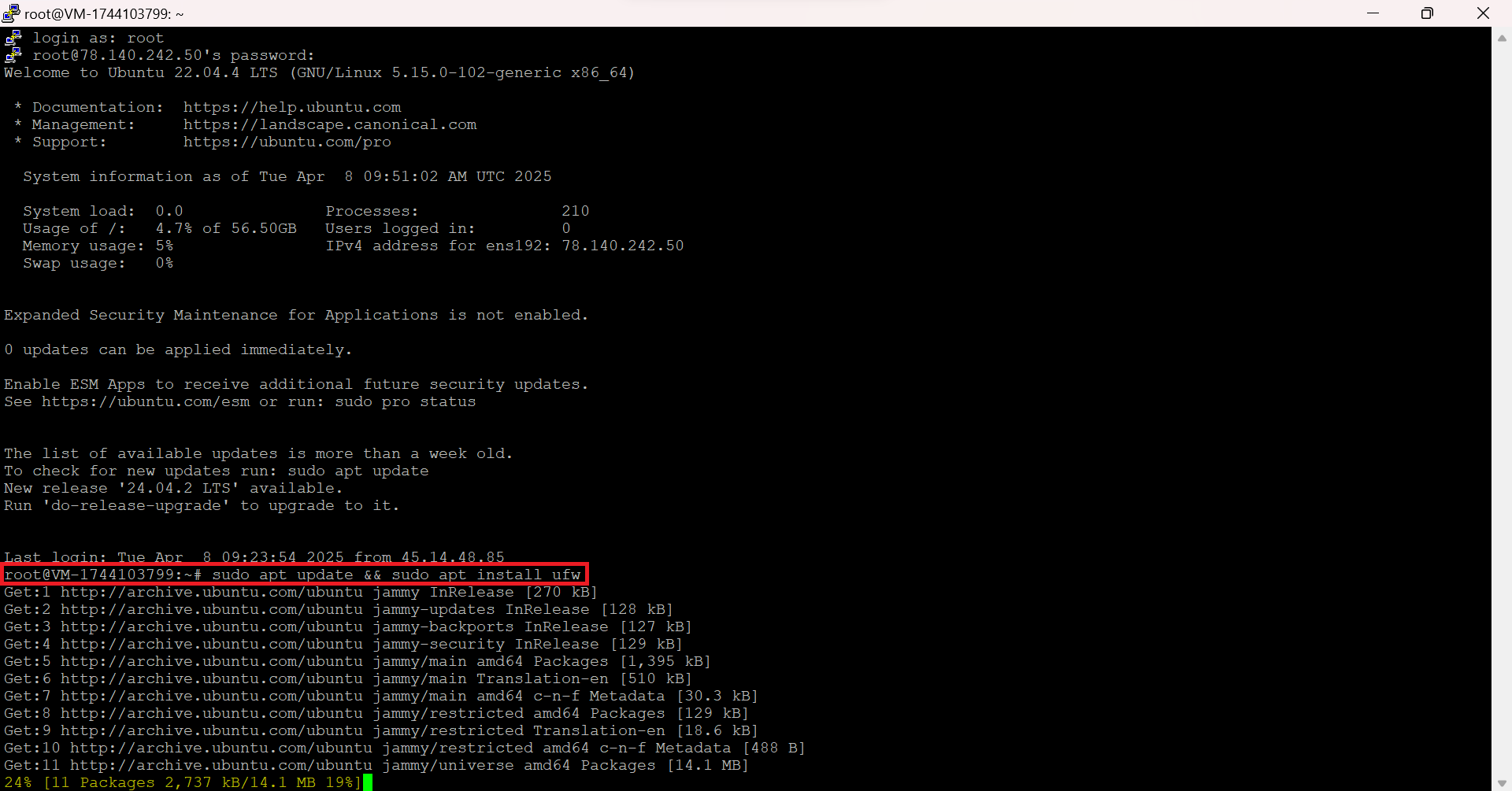
Checking UFW Firewall Status on Ubuntu
To check whether the firewall is active:
sudo ufw statusIf you see Status: inactive, it means the firewall is currently disabled.
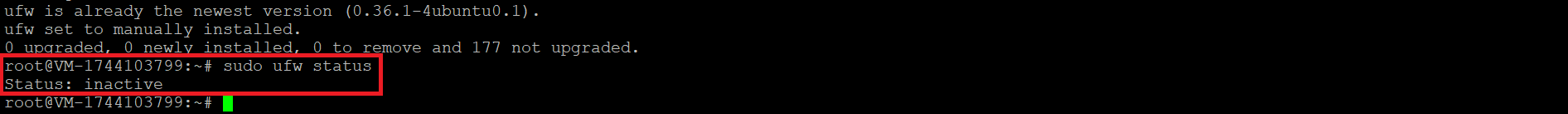
Enabling UFW
To enable UFW:
sudo ufw allow OpenSSHsudo ufw enable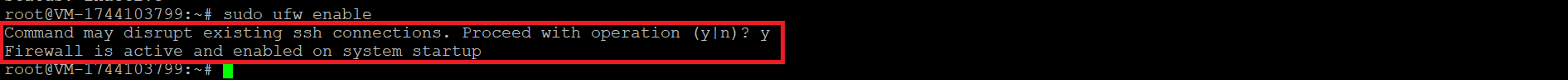
To see the list of current rules:
sudo ufw status verbose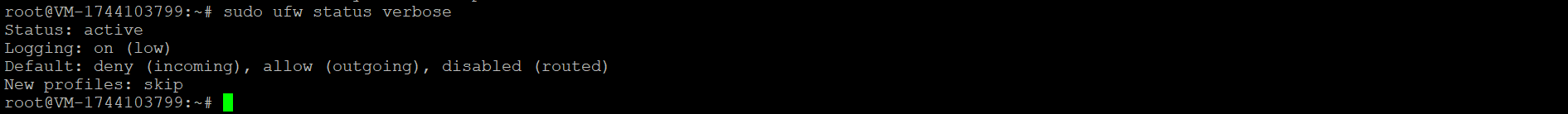
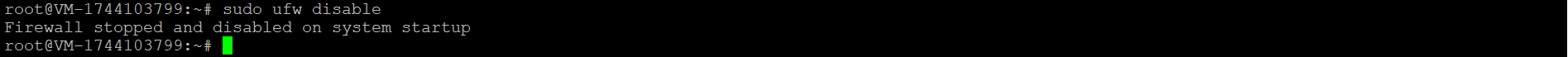
Disabling UFW
To temporarily disable the firewall:
sudo ufw disableNote: This completely turns off your firewall—use with caution!
Blocking IP Addresses and Subnets
- Block a specific IP:
sudo ufw deny from 91.198.174.190 - Block an entire subnet:
sudo ufw deny from 91.198.174.0/24 - Block an IP on a specific interface:
sudo ufw deny in on eth0 from 91.198.174.192 Allowing IP Addresses
- Allow all traffic from a specific IP:
sudo ufw allow from 91.198.174.192 - Allow incoming traffic from an IP on a specific interface:
sudo ufw allow in on eth0 from 91.198.174.22 Deleting Rules
- Delete a rule by its parameters:
sudo ufw delete allow from 91.198.174.192 - Delete a rule by number:
sudo ufw status numbered sudo ufw delete 1 Application Profiles
UFW can use predefined profiles for common services:
- List available profiles:
sudo ufw app list - Enable a profile (e.g. OpenSSH):
sudo ufw allow OpenSSH - Remove a profile:
sudo ufw delete allow "Nginx Full" 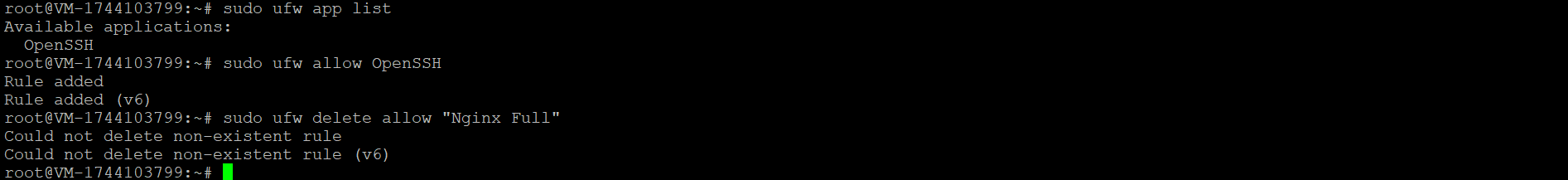
Opening Common Ports
- SSH (port 22):
sudo ufw allow 22 - HTTP (port 80):
sudo ufw allow http - HTTPS (port 443):
sudo ufw allow https - HTTP + HTTPS combined:
sudo ufw allow proto tcp from any to any port 80,443 Allowing Database Connections
- MySQL (port 3306):
sudo ufw allow from 91.198.174.33 to any port 3306 - PostgreSQL (port 5432):
sudo ufw allow from 91.198.174.33 to any port 5432 - Allow for a subnet:
sudo ufw allow from 91.198.174.0/24 to any port 3306 FAQ: UFW (Uncomplicated Firewall) on Ubuntu
- Q1: What is the safest order to enable UFW on a remote server?
A: Set defaults → allow SSH → enable.sudo ufw default deny incomingsudo ufw default allow outgoingsudo ufw allow OpenSSHsudo ufw enable - Q2: How do I audit what’s currently allowed?
A:sudo ufw status verboseOr with numbering:
sudo ufw status numbered - Q3: What if I blocked SSH and lost access?
A: Use your hosting provider console (KVM/serial/web console), then run:sudo ufw allow OpenSSHOr temporarily disable UFW:
sudo ufw disable - Q4: Can I rate-limit SSH instead of just allowing it?
A: Yes, this is a common hardening step:sudo ufw limit OpenSSH(or sudo ufw limit 22/tcp)
- Q5: How do I allow multiple ports cleanly?
A:sudo ufw allow 80,443/tcpOr ranges:
sudo ufw allow 60000:61000/udp - Q6: How do I make UFW apply to IPv6 too?
A: In /etc/default/ufw, set:
IPV6=yes
Then reload:sudo ufw reload - Q7: Why is exposing MySQL/PostgreSQL to “any” a bad idea?
A: Databases are high-value targets. Allow them only from trusted IPs/subnets (or private networks/VPN). Example:sudo ufw allow from 91.198.174.33 to any port 5432 proto tcp - Q8: How do I remove the wrong rule quickly?
A:sudo ufw status numberedsudo ufw delete <rule_number> - Q9: How do I turn on UFW logs?
A:sudo ufw logging onTo see log level:
sudo ufw status verbose
UFW Best Practices for Ubuntu Servers
UFW best practices for Ubuntu servers:
- Allow SSH before enabling UFW (prefer limit instead of allow to reduce brute-force attempts).
- Set a safe baseline: deny incoming by default, allow outgoing, then open only what you need.
- Never expose databases to the internet — allow MySQL/PostgreSQL only from trusted IPs or private networks.
- Enable logging and periodically audit rules to remove outdated exceptions.
- If you use IPv6, ensure it’s enabled in UFW (IPV6=yes) so rules protect both stacks.
- Use a provider console (KVM/serial) as a fallback in case you lock yourself out.
Conclusion
UFW is a simple and reliable way to harden an Ubuntu server by controlling inbound and outbound traffic without dealing directly with raw iptables rules. In this guide, you installed UFW, checked status, safely enabled the firewall without losing SSH access, and learned how to allow or block ports, IPs, subnets, and service profiles.
For a secure setup, start with a restrictive default policy, expose only required services (SSH/HTTP/HTTPS), limit access to sensitive ports like databases, and regularly review rules and logs — especially if your server uses both IPv4 and IPv6.




