Restoring a root password via Recovery Boot
This instruction describes how to use a recovery image to restore a password for a root user.
Password recovery
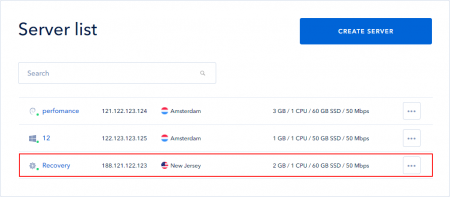
First, open the server that you want to restore the root password for, from the server list.
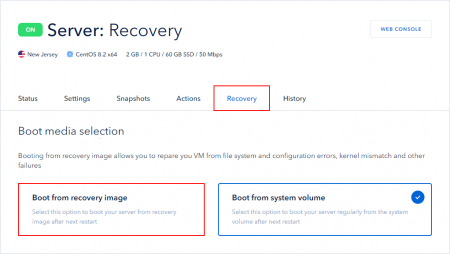
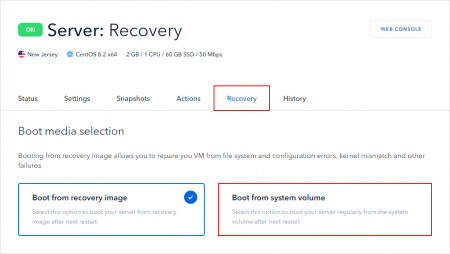
Open a Recovery tab and select “Boot from the recovery image”.
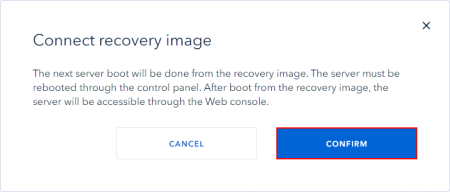
Confirm a connection to the recovery image.
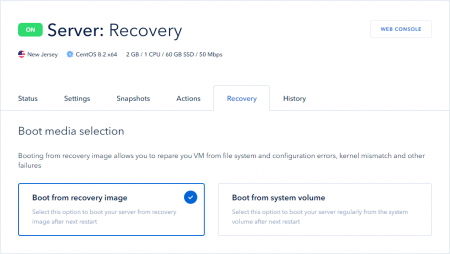
The boot type will be changed.
Important: after booting from the recovery image, the server will be accessible via a Web console!
To boot from the recovery image, you must restart the server from the control panel or using OS tools. Next, let's look at an example of a reboot from the control panel.
Go to the Actions —> Power tab and restart the server.
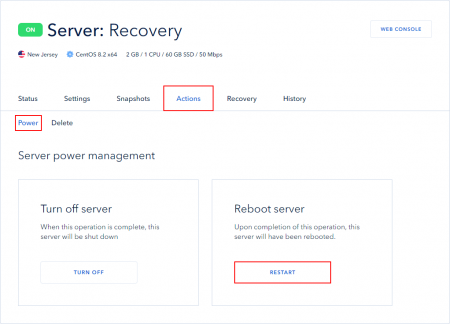
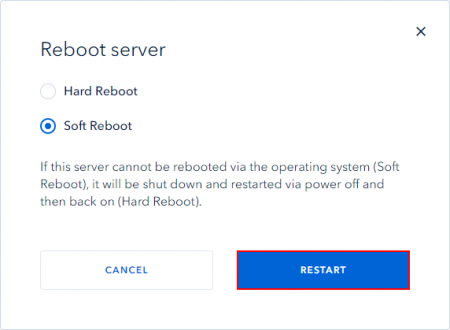
Confirm the server reboot.
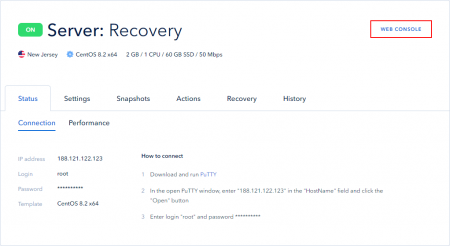
After restarting the server, open the Web console.
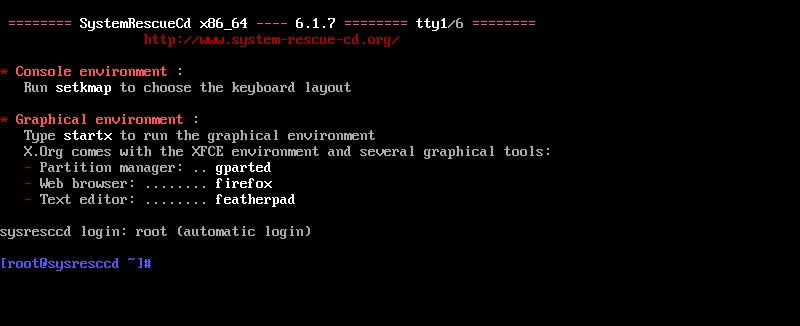
Select the first option *Boot SystemRescueCd using the default options.
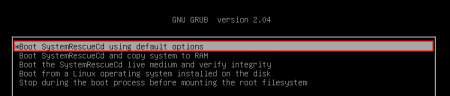
If a command line has been already displayed in the console, the boot option was selected by default.
Next, you need to find out which disk partition has got the system:
fdisk -l
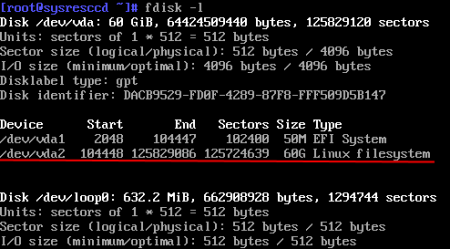
In this case, it is /dev/vda2/.
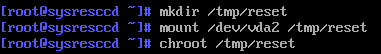
Create a temporary directory for a new system:mkdir /tmp/reset
Mount the system partition to the created folder:mount /dev/vda2 /tmp/reset
Change the root directory to a new one: chroot /tmp/reset
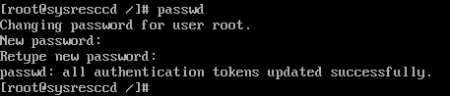
To change the root password, run the following command:passwd
Enter and confirm your new password.
PAY ATTENTION: When entering a password, the password characters are not displayed, but they are still entered!
Change the recovery image boot to the system boot in the Recovery tab in the control panel.
Restart the server from the control panel.
After restarting the server, connect to the server with a new password as usual.
 700
300
700
300
 700
300
700
300
 700
300
700
300


